【更新】2019年1月24日06:00。iMac 27-inch, Late 2013、Macbook Retina, 12-inch, Early 2016のアップデートサイズ・所要時間の情報を追記しました。
2019年1月23日。macOSの最新版10.14.3がリリースされました。アップデートすべきか否か、修正された内容、アップデートのサイズと所要時間、更新後の不具合等についての情報を紹介します。
macOS Mojave 10.14.3へのアップデート後の不具合の有無について
追記2019年1月24日06:00現在、- macOS Mojave 10.14.2のiPad 27-inch, Late 2013にmacOS Mojave 10.14.3をインストールしたことろ問題は発生していません。
- macOS Mojave 10.14.2のMacbook Retina Early 2016にmacOS Mojave 10.14.3をインストールしたことろ問題は発生していません。
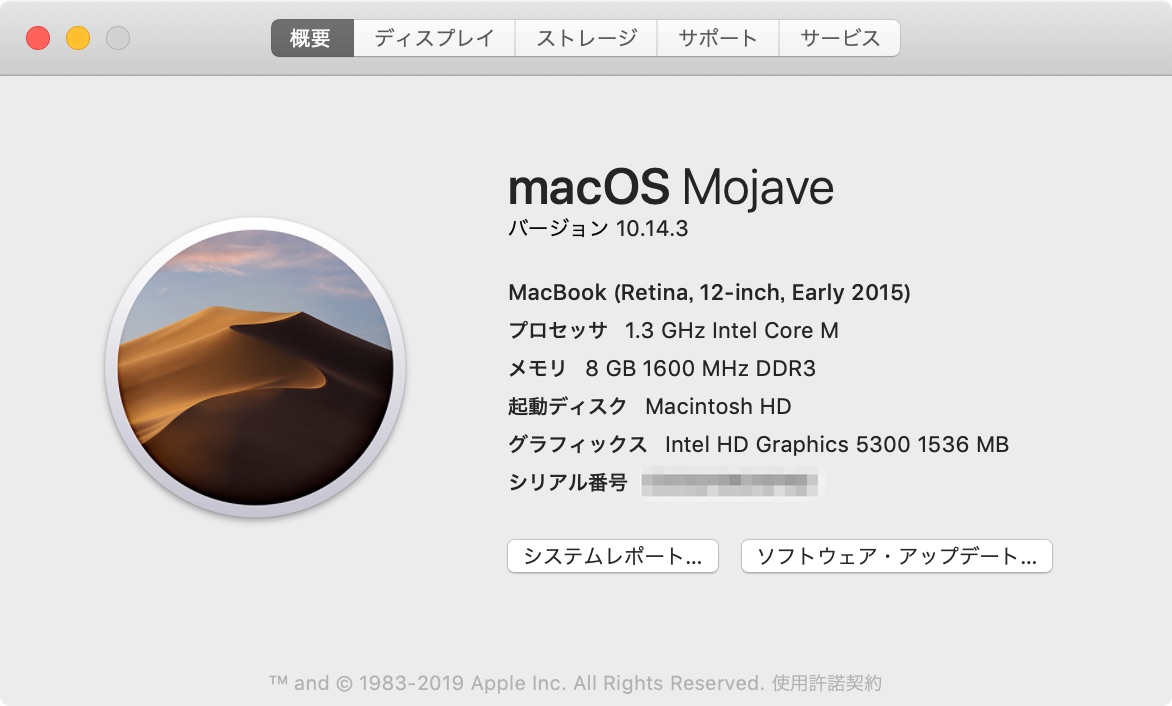
- macOS Mojave 10.14.2のMacbook Retina Early 2015にmacOS Mojave 10.14.3をインストールしたことろ問題は発生していません。
macOS Mojave 10.14.3 アップデートすべき?待つべき?
macOS Mojave 10.14.3は3番目の数字が2→3への変更となっており、メンテナンスリリースの位置づけとなっています。macOS Mojave 10.14.3 にアップデートしても良い人
次の方はmacOS Mojave 10.14.3にアップデートすることを推奨します。- すでにmacOS Mojave 10.14 以降を利用している方
- そろそろmacOS Mojaveにアップデートしようと考えている方
macOS Mojave 10.14.3 へのアップデートを待ったほうが良い方
次の方はmacOS Mojave 10.14.3へのアップデートは待つことを推奨します。- 心配性、不安症な方
- macOS Mojave対象機種以外の方
- 古いアプリケーションを使用している方
macOS Mojave 10.14.3 のサイズ、アップデート所要時間は?
macOS Mojave 10.14.3のサイズ、アップデート所要時間は次のとおりです。| 機種 | サイズ | 全体 所要時間 | ダウンロード 所要時間 | インストール 所要時間 |
|---|---|---|---|---|
| Macbook Retina, 12-inch, Early 2015 | 1.97GB | 25分 | 4分 (有線LAN) | 20分 |
| 追記iPad 27-inch, Late 2013 | 1.97GB | 20分 | 5分 (有線LAN) | 15分 |
| 追記Macbook Retina, 12-inch, Early 2016 | 1.97GB | 23分 | 6分 (Wi-Fi) | 17分 |
- 安定・高速なWi-FI接続、または、有線LAN
- 電源
macOS Mojave 10.14.3 修正内容
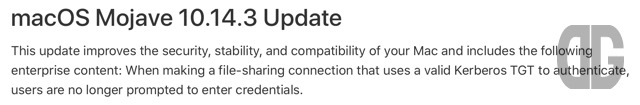 Appleの公式サイト「macOS Mojave のアップデートの新機能」には2019年1月23日現在、macOS Mojave 10.14.3の情報は掲載されていません。
なので、英語版の「What’s new in the updates for macOS Mojave」の「macOS Mojave 10.14.3 Update」の情報を紹介します。
Appleの公式サイト「macOS Mojave のアップデートの新機能」には2019年1月23日現在、macOS Mojave 10.14.3の情報は掲載されていません。
なので、英語版の「What’s new in the updates for macOS Mojave」の「macOS Mojave 10.14.3 Update」の情報を紹介します。
This update improves the security, stability, and compatibility of your Mac and includes the following enterprise content: When making a file-sharing connection that uses a valid Kerberos TGT to authenticate, users are no longer prompted to enter credentials.これによると
- セキュリティ、安定性、互換性の改善
- エンタープライズ向けのケルベロス認証を用いるファイル共有作成時、認証が求められない不具合への対応
macOS Mojave 10.14.3 セキュリティアップデートについて
macOS Mojave 10.14.3で18件のセキュリティ対応を実施しています。 2019年1月23日15:00現在、公式サイト「Apple セキュリティアップデート」にはmacOS 10.14.3に関する日本語の情報が記載されていません。 そのため、英語版の「About the security content of macOS Mojave 10.14.3, Security Update 2019-001 High Sierra, Security Update 2019-001 Sierra」の内容を確認します。macOS Mojave 10.14.3, Security Update 2019-001 High Sierra, Security Update 2019-001 SierraReleased January 22, 2019 AppleKeyStoreBluetooth
- Available for: macOS Mojave 10.14.2
- Impact: A sandboxed process may be able to circumvent sandbox restrictions
- Description: A memory corruption issue was addressed with improved validation.
- CVE-2019-6235: Brandon Azad
Core Media
- Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: An attacker in a privileged network position may be able to execute arbitrary code
- Description: An out-of-bounds read was addressed with improved input validation.
- CVE-2019-6200: an anonymous researcher
CoreAnimation
- Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may be able to elevate privileges
- Description: An out-of-bounds read was addressed with improved bounds checking.
- CVE-2019-6202: Fluoroacetate working with Trend Micro’s Zero Day Initiative
- CVE-2019-6221: Fluoroacetate working with Trend Micro’s Zero Day Initiative
CoreAnimation
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may be able to read restricted memory
- Description: An out-of-bounds read was addressed with improved bounds checking.
- CVE-2019-6231: Zhuo Liang of Qihoo 360 Nirvan Team
FaceTime
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may be able to break out of its sandbox
- Description: A memory initialization issue was addressed with improved memory handling.
- CVE-2019-6230: Proteas, Shrek_wzw and Zhuo Liang of Qihoo 360 Nirvan Team
Hypervisor
- Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A remote attacker may be able to initiate a FaceTime call causing arbitrary code execution
- Description: A buffer overflow issue was addressed with improved memory handling.
- CVE-2019-6224: Natalie Silvanovich of Google Project Zero
Intel Graphics Driver
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
- Impact: A malicious application may be able to elevate privileges
- Description: A memory corruption issue was addressed with improved state management.
- CVE-2018-4467: Martim Carbone, David Vernet, Sam Scalise, and Fred Jacobs of the Virtual Machine Monitor Group of VMware, Inc.
IOKit
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
- Impact: A malicious application may be able to execute arbitrary code with system privileges
- Description: A memory consumption issue was addressed with improved memory handling.
- CVE-2018-4452: Liu Long of Qihoo 360 Vulcan Team
Kernel
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may be able to break out of its sandbox
- Description: A type confusion issue was addressed with improved memory handling.
- CVE-2019-6214: Ian Beer of Google Project Zero
Kernel
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may be able to elevate privileges
- Description: A memory corruption issue was addressed with improved validation.
- CVE-2019-6225: Brandon Azad of Google Project Zero, Qixun Zhao of Qihoo 360 Vulcan Team
Kernel
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may be able to execute arbitrary code with kernel privileges
- Description: A memory corruption issue was addressed with improved input validation.
- CVE-2019-6210: Ned Williamson of Google
Kernel
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may cause unexpected changes in memory shared between processes
- Description: A memory corruption issue was addressed with improved lock state checking.
- CVE-2019-6205: Ian Beer of Google Project Zero
Kernel
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: An application may be able to execute arbitrary code with kernel privileges
- Description: A buffer overflow was addressed with improved bounds checking.
- CVE-2019-6213: Ian Beer of Google Project Zero
Kernel
- Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may be able to determine kernel memory layout
- Description: An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation.
- CVE-2019-6209: Brandon Azad of Google Project Zero
libxpc
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may cause unexpected changes in memory shared between processes
- Description: A memory initialization issue was addressed with improved memory handling.
- CVE-2019-6208: Jann Horn of Google Project Zero
Natural Language Processing
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: A malicious application may be able to execute arbitrary code with kernel privileges
- Description: A memory corruption issue was addressed with improved input validation.
- CVE-2019-6218: Ian Beer of Google Project Zero
QuartzCore
- Available for: macOS Mojave 10.14.2
- Impact: Processing a maliciously crafted message may lead to a denial of service
- Description: A denial of service issue was addressed with improved validation.
- CVE-2019-6219: Authier Thomas
SQLite
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.2
- Impact: An application may be able to read restricted memory
- Description: An out-of-bounds read was addressed with improved input validation.
- CVE-2019-6220: Yufeng Ruan of Chaitin Security Research Lab
WebRTC
- Available for: macOS Mojave 10.14.2
- Impact: A maliciously crafted SQL query may lead to arbitrary code execution
- Description: Multiple memory corruption issues were addressed with improved input validation.
- CVE-2018-20346: Tencent Blade Team
- CVE-2018-20505: Tencent Blade Team
- CVE-2018-20506: Tencent Blade Team
- Available for: macOS Mojave 10.14.2
- Impact: Processing maliciously crafted web content may lead to arbitrary code execution
- Description: A memory corruption issue was addressed with improved state management.
- CVE-2019-6211: Georgi Geshev (@munmap), Fabi Beterke (@pwnfl4k3s), and Rob Miller (@trotmaster99) of MWR Labs (@mwrlabs) working with Trend Micro’s Zero Day Initiative
 Additional recognitionapache_mod_php
Additional recognitionapache_mod_phpWe would like to acknowledge an anonymous researcher for their assistance.
KernelWe would like to acknowledge Daniel Roethlisberger of Swisscom CSIRT for their assistance.
LibreSSLWe would like to acknowledge Viktor Szakats for their assistance.
mDNSResponderWe would like to acknowledge Fatemah Alharbi of University of California, Riverside (UCR) and Taibah University (TU), Jie Chang of LinkSure Network, Yuchen Zhou of Northeastern University, Feng Qian of University of Minnesota – Twin City, Zhiyun Qian of University of California, Riverside (UCR), and Nael Abu-Ghazaleh of University of California, Riverside (UCR) for their assistance.
Information about products not manufactured by Apple, or independent websites not controlled or tested by Apple, is provided without recommendation or endorsement. Apple assumes no responsibility with regard to the selection, performance, or use of third-party websites or products. Apple makes no representations regarding third-party website accuracy or reliability. Risks are inherent in the use of the Internet. Contact the vendor for additional information. Other company and product names may be trademarks of their respective owners.公開日:
macOS Mojave 10.14.3 手動アップデート手順
macOS Mojave 10.14.3への手動でのアップデート手順は次の通りです。 1.歯車マークの「システム環境設定」アイコンをクリックします。 2.「ソフトウェア アップデート」アイコンをクリックします。 3.「ソフトウェア・アップデート」画面で「このMac用のアップデートがあります」と表示されていることを確認します。
3.「ソフトウェア・アップデート」画面で「このMac用のアップデートがあります」と表示されていることを確認します。
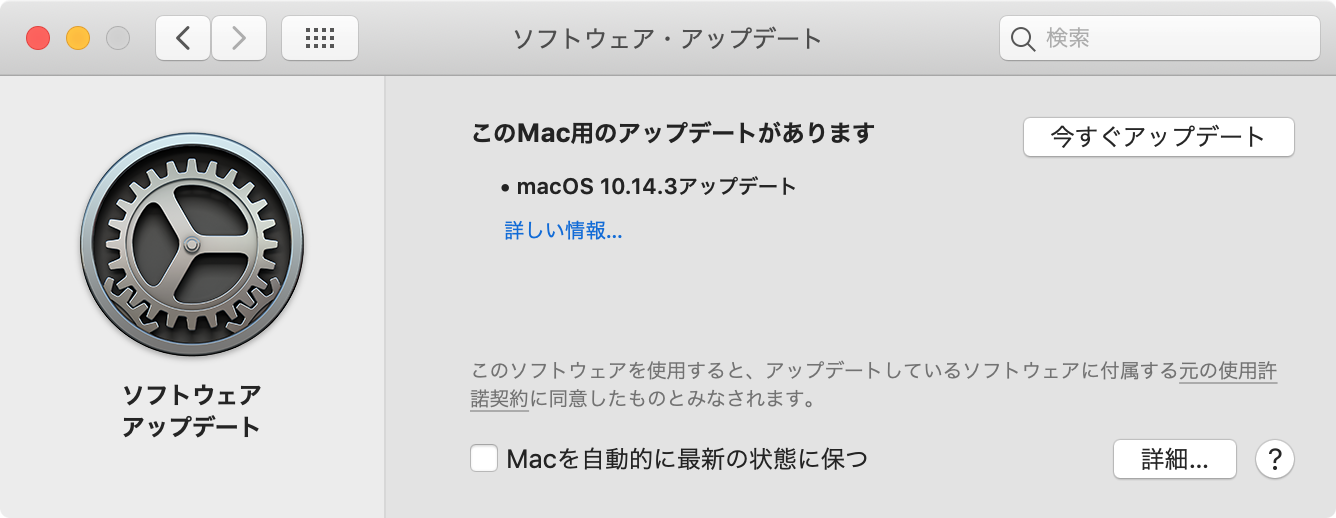 ※表示されない場合は画面下の「Macを自動的に最新の状態に保つ」のチェックボックスにチェックを付けたり外したりすると内容が更新される場合があります。
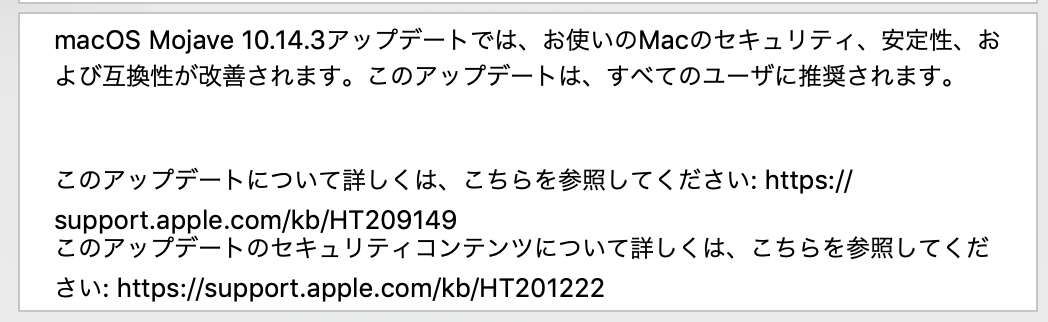
またこのとき、「詳しい情報…」のリンクをクリックするとmacOS 10.14.3 の更新内容が表示されます。
※表示されない場合は画面下の「Macを自動的に最新の状態に保つ」のチェックボックスにチェックを付けたり外したりすると内容が更新される場合があります。
またこのとき、「詳しい情報…」のリンクをクリックするとmacOS 10.14.3 の更新内容が表示されます。
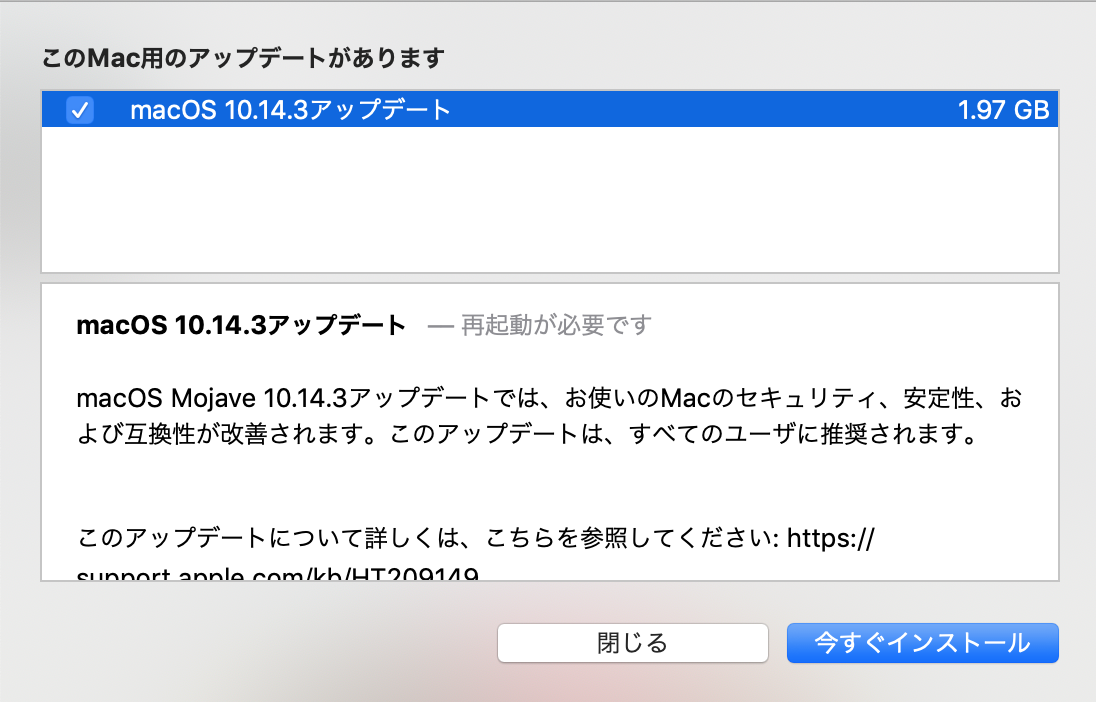 画面に表示されない部分はスクロールできます。
画面に表示されない部分はスクロールできます。
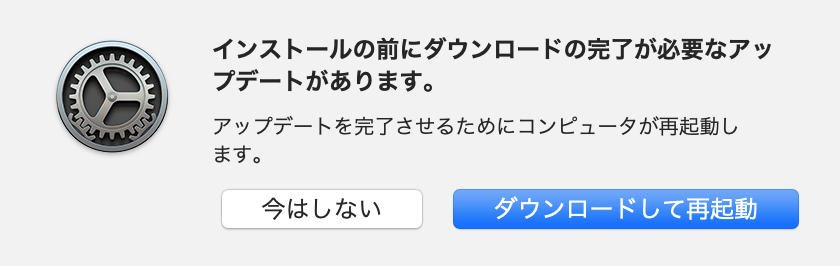
 5.元の画面にもどり「今すぐアップデート」ボタンをクリックすると確認画面が表示されるので「ダウンロードして再起動」ボタンをクリックします。
5.元の画面にもどり「今すぐアップデート」ボタンをクリックすると確認画面が表示されるので「ダウンロードして再起動」ボタンをクリックします。
 6.macOS 10.14.3 のダウンロードが始まります。
6.macOS 10.14.3 のダウンロードが始まります。
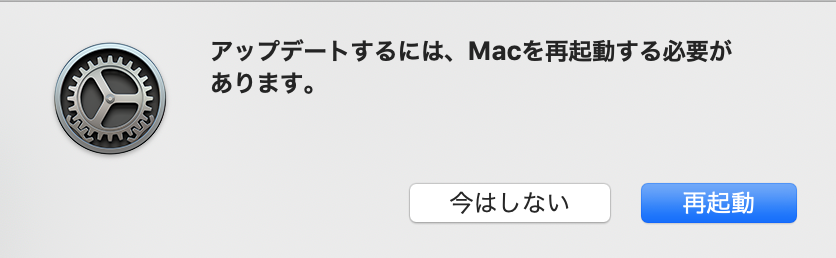
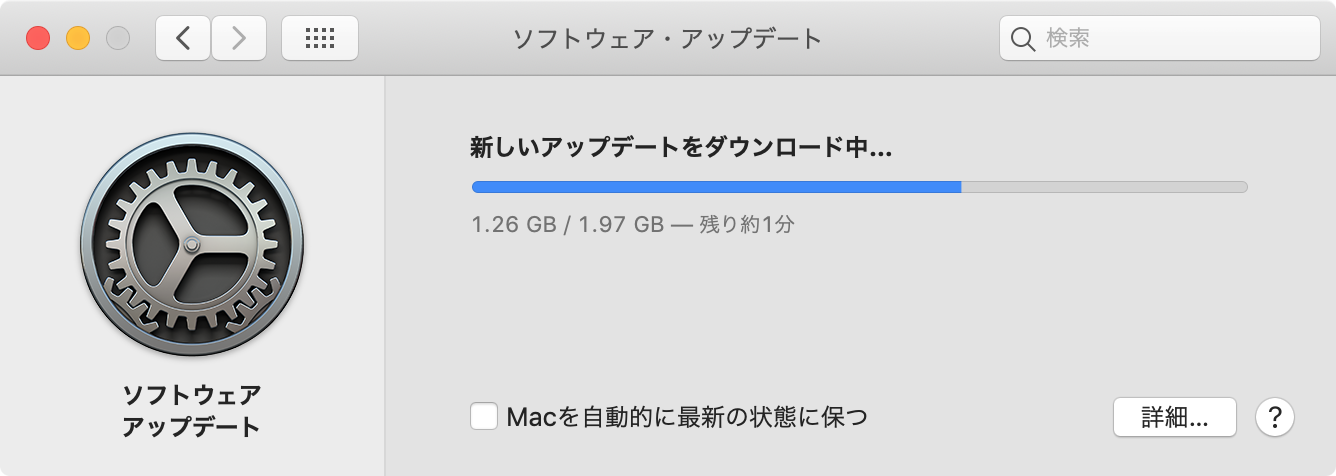 7.5分程度ダウンロードが行われ、ダウンロード完了後、再度「今すぐインストール」ボタンをクリックすると確認画面が表示されるので「再起動」をクリックします。
7.5分程度ダウンロードが行われ、ダウンロード完了後、再度「今すぐインストール」ボタンをクリックすると確認画面が表示されるので「再起動」をクリックします。
 8.インストールが開始され、再起動が何回か行われたあと10分程度のあと、ログイン画面が表示されるのでログインします。
8.インストールが開始され、再起動が何回か行われたあと10分程度のあと、ログイン画面が表示されるのでログインします。
 9.スタートメニューの右上のリンゴマークをクリックし「このMacについて」をクリックし、 macOS Mojaveのバージョンが「10.14.3」と表示されることを確認すればアップデート完了です! ]]>
9.スタートメニューの右上のリンゴマークをクリックし「このMacについて」をクリックし、 macOS Mojaveのバージョンが「10.14.3」と表示されることを確認すればアップデート完了です! ]]>