本記事では、アップデートすべきか否か、修正された内容、アップデートのサイズ・所要時間、ならびにアップデート後の不具合について調査・体験した情報を記載しています。
目次
macOS Mojave 10.14.4 アップデートすべき?待つべき?
macOS Mojave 10.14.4は3番目の数字が3→4への変更となるメンテナンスリリースの位置づけとなっています。 が、iPhoneと違って、macOS Mojaveでは新機能の追加なども含まれるため、アップデートにはちょっとだけ気をつけた方が良いかもしれません。 とは言え、個人的にはmacOSのメンテナンスリリースでは大きな不具合に遭遇したことがないので、TimeMachineでバックアップしている方は、最新 パックアップ採取後、インストールしても良いと考えています。 万一不具合が発生したらTimeMachineからリストアすればいいし。 TimeMachineによるバックアップ環境がない方もそれほど恐れる必要はないと考えていますが、心配な方はまずは1週間大きな不具合化ないかウォッチしましょう。macOS Mojave 10.14.4へのアップデート後の不具合の有無について
2019年3月27日11:00現在、- macOS Mojave 10.14.3のMacBook Retina Early 2015をmacOS Mojave 10.14.4にアップデート
- macOS Mojave 10.14.3のiPad 27-inch, Late 2013をmacOS Mojave 10.14.4にアップデート
- macOS Mojave 10.14.3のMacBook Pro (13-inch, 2016, Thow Thunderboldt 3 ports)をmacOS Mojaveにアップデート
- 文鎮になる(起動しない)
- 再起動を繰り返す
- 通信できない
macOS Mojave 10.14.4 のサイズ、アップデート所要時間は?
macOS Mojave 10.14.4のサイズ、アップデート所要時間は次のとおりです。| 機種 | サイズ | 全体 所要時間 | ダウンロード 所要時間 | インストール 所要時間 |
|---|---|---|---|---|
| Macbook Retina, 12-inch, Early 2015 | 2.5GB | 52分 | 17分 (有線LAN) | 35分 |
| IMac 27-inch, Late 2013 | 2.5GB | (不明) | 不明 (有線LAN) | 不明 |
| MacBook Pro (13-inch, 2016, Two Thunderbolt 3 ports) | 2.71GB (※) | 25分 | 5分 (有線LAN) | 20分 |
- 安定・高速なWi-FI接続、または、有線LAN
- 電源
macOS Mojave 10.14.4の修正内容について
Appleの公式サイト「macOS Mojave のアップデートの新機能」には2019年3月27日13:30現在、macOS Mojave 10.14.4の情報は掲載されていません。 なので、英語版の「What’s new in the updates for macOS Mojave」の「macOS 10.14.4」の情報を紹介します。macOS 10.14.4これによるとThis update:Enterprise content:
- Apple News+1
- Apple News+ is a new subscription service that extends the Apple News experience with hundreds of magazines and top newspapers.
- Our editors handpick top articles and magazine issues, and you also get personalized recommendations on the topics most interesting to you.
- Automatic downloads make it easy to read magazine issues offline.
- Apple News is now available in Canada, with a free experience that includes handpicked Top Stories, a personalized Today feed, and support for both English and French.
- Apple News+ is available in the U.S. and in Canada, with dozens of additional Canadian magazines.
- Safari
- Adds Dark Mode support for websites that support custom color schemes.
- Streamlines website login when filling credentials with Password AutoFill.
- Allows push notification prompts only after interacting with a website.
- Adds a warning when an insecure webpage is loaded.
- Removes support for the expired Do Not Track standard to prevent potential use as a fingerprinting variable; Intelligent Tracking Prevention now protects against cross-site tracking by default.
- iTunes
- Shows more editorial highlights on a single page in the Browse tab, making it easier to discover new music, playlists, and more in Apple Music.
- AirPods
- Adds support for new AirPods (2nd generation).
- More:
- Supports Air Quality Index in Maps for US, UK, and India.
- Improves the quality of audio recordings in Messages.
- Supports real-time text (RTT) for phone calls made through a nearby iPhone on Mac.2
- Provides enhanced support for external GPUs in Activity Monitor.
- Fixes an App Store issue that may have prevented adoption of the latest versions of Pages, Keynote, Numbers, iMovie, and GarageBand.
- Improves the reliability of USB audio devices when used with MacBook Air, MacBook Pro, and Mac mini models introduced in 2018.
- Corrects the default screen brightness for the MacBook Air introduced in 2018.
- Fixes a graphics compatibility issue that may occur on some external displays connected to Mac mini (2018).
- Resolves Wi-Fi connection issues that may occur after upgrading to macOS Mojave.
- Fixes an issue where re-adding an Exchange account may cause it to disappear from Internet Accounts.
- Fixes an issue where AOL user passwords may be frequently requested in Mail.
- Fixes an issue that could prevent mobile accounts from logging in from an off-network Mac after changing their network account password.
- Fixes an issue that intermittently prevented apps from downloading from the App Store or installing via MDM.
- Mobile Active Directory accounts that have used their personal recovery key (PRK) to unlock a FileVault volume are no longer required to continue using the PRK to unlock, but can use their login password instead.
- Apple News+への対応(日本未対応)
- Safariの改善(ダークモードへの対応含む)
- iTunesの改善
- 第2世代AirPodsへの対応
- その他2018年モデルのデバイス関連不具合やWi-Fi接続の不具合への対応
macOS Mojave 10.14.4 セキュリティアップデートについて
macOS Mojave 10.14.4で35件のセキュリティ対応を実施しています。 2019年3月27日13:30現在、公式サイト「Apple セキュリティアップデート」にはmacOS 10.14.4に関する日本語の情報が記載されていません。 そのため、英語版の「About the security content of macOS Mojave 10.14.4, Security Update 2019-002 High Sierra, Security Update 2019-002 Sierra」の内容を確認します。 タイトルからmacOS High SIerra 10.13系、macOS Sierra 10.12系のセキュリティアップデートも提供されていることが伺えます。macOS Mojave 1 0.14.4, Security Update 2019-002 High Sierra, Security Update 2019-002 SierraReleased March 25, 2019 AppleGraphicsControlBom
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: A malicious application may be able to execute arbitrary code with kernel privileges
- Description: A buffer overflow was addressed with improved size validation.
- CVE-2019-8555: Zhiyi Zhang of 360 ESG Codesafe Team, Zhuo Liang and shrek_wzw of Qihoo 360 Nirvan Team
CFString
- Available for: macOS Mojave 10.14.3
- Impact: A malicious application may bypass Gatekeeper checks
- Description: This issue was addressed with improved handling of file metadata.
- CVE-2019-6239: Ian Moorhouse and Michael Trimm
configd
- Available for: macOS Mojave 10.14.3
- Impact: Processing a maliciously crafted string may lead to a denial of service
- Description: A validation issue was addressed with improved logic.
- CVE-2019-8516: SWIPS Team of Frifee Inc.
Contacts
- Available for: macOS Mojave 10.14.3
- Impact: A malicious application may be able to elevate privileges
- Description: A memory initialization issue was addressed with improved memory handling.
- CVE-2019-8552: Mohamed Ghannam (@_simo36)
CoreCrypto
- Available for: macOS Mojave 10.14.3
- Impact: A malicious application may be able to elevate privileges
- Description: A buffer overflow issue was addressed with improved memory handling.
- CVE-2019-8511: an anonymous researcher
DiskArbitration
- Available for: macOS Mojave 10.14.3
- Impact: A malicious application may be able to elevate privileges
- Description: A buffer overflow was addressed with improved bounds checking.
- CVE-2019-8542: an anonymous researcher
FaceTime
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: An encrypted volume may be unmounted and remounted by a different user without prompting for the password
- Description: A logic issue was addressed with improved state management.
- CVE-2019-8522: Colin Meginnis (@falc420)
Feedback Assistant
- Available for: macOS Mojave 10.14.3
- Impact: A user’s video may not be paused in a FaceTime call if they exit the FaceTime app while the call is ringing
- Description: An issue existed in the pausing of FaceTime video. The issue was resolved with improved logic.
- CVE-2019-8550: Lauren Guzniczak of Keystone Academy
Feedback Assistant
- Available for: macOS Mojave 10.14.3
- Impact: A malicious application may be able to gain root privileges
- Description: A race condition was addressed with additional validation.
- CVE-2019-8565: CodeColorist of Ant-Financial LightYear Labs
file
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: A malicious application may be able to overwrite arbitrary files
- Description: This issue was addressed with improved checks.
- CVE-2019-8521: CodeColorist of Ant-Financial LightYear Labs
Graphics Drivers
- Available for: macOS Mojave 10.14.3
- Impact: Processing a maliciously crafted file might disclose user information
- Description: An out-of-bounds read was addressed with improved bounds checking.
- CVE-2019-6237: an anonymous researcher
iAP
- Available for: macOS Mojave 10.14.3
- Impact: An application may be able to read restricted memory
- Description: An out-of-bounds read was addressed with improved bounds checking.
- CVE-2019-8519: Aleksandr Tarasikov (@astarasikov), Juwei Lin (@panicaII), and Junzhi Lu of Trend Micro Research working with Trend Micro’s Zero Day Initiative
IOGraphics
- Available for: macOS Mojave 10.14.3
- Impact: A malicious application may be able to elevate privileges
- Description: A buffer overflow was addressed with improved bounds checking.
- CVE-2019-8542: an anonymous researcher
IOHIDFamily
- Available for: macOS Mojave 10.14.3
- Impact: A Mac may not lock when disconnecting from an external monitor
- Description: A lock handling issue was addressed with improved lock handling.
- CVE-2019-8533: an anonymous researcher, James Eagan of Télécom ParisTech, R. Scott Kemp of MIT, and Romke van Dijk of Z-CERT
IOKit
- Available for: macOS Mojave 10.14.3
- Impact: A local user may be able to cause unexpected system termination or read kernel memory
- Description: A memory corruption issue was addressed with improved state management.
- CVE-2019-8545: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
IOKit SCSI
- Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: A local user may be able to read kernel memory
- Description: A memory initialization issue was addressed with improved memory handling.
- CVE-2019-8504: an anonymous researcher
Kernel
- Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: An application may be able to execute arbitrary code with kernel privileges
- Description: A memory corruption issue was addressed with improved input validation.
- CVE-2019-8529: Juwei Lin (@panicaII) of Trend Micro
Kernel
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: A remote attacker may be able to cause unexpected system termination or corrupt kernel memory
- Description: A buffer overflow was addressed with improved size validation.
- CVE-2019-8527: Ned Williamson of Google and derrek (@derrekr6)
Kernel
- Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
- Impact: Mounting a maliciously crafted NFS network share may lead to arbitrary code execution with system privileges
- Description: A buffer overflow was addressed with improved bounds checking.
- CVE-2019-8508: Dr. Silvio Cesare of InfoSect
Kernel
- Available for: macOS Mojave 10.14.3
- Impact: An application may be able to gain elevated privileges
- Description: A logic issue was addressed with improved state management.
- CVE-2019-8514: Samuel Groß of Google Project Zero
Kernel
- Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
- Impact: A malicious application may be able to determine kernel memory layout
- Description: A memory initialization issue was addressed with improved memory handling.
- CVE-2019-8540: Weibo Wang (@ma1fan) of Qihoo 360 Nirvan Team
Kernel
- Available for: macOS Mojave 10.14.3
- Impact: A local user may be able to read kernel memory
- Description: A memory corruption issue was addressed with improved memory handling.
- CVE-2019-7293: Ned Williamson of Google
Messages
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: A malicious application may be able to determine kernel memory layout
- Description: An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation.
- CVE-2019-6207: Weibo Wang of Qihoo 360 Nirvan Team (@ma1fan)
- CVE-2019-8510: Stefan Esser of Antid0te UG
Notes
- Available for: macOS Mojave 10.14.3
- Impact: A local user may be able to view sensitive user information
- Description: An access issue was addressed with additional sandbox restrictions.
- CVE-2019-8546: ChiYuan Chang
PackageKit
- Available for: macOS Mojave 10.14.3
- Impact: A local user may be able to view a user’s locked notes
- Description: An access issue was addressed with improved memory management.
- CVE-2019-8537: Greg Walker (gregwalker.us)
Perl
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: A malicious application may be able to elevate privileges
- Description: A logic issue was addressed with improved validation.
- CVE-2019-8561: Jaron Bradley of Crowdstrike
Power Management
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: Multiple issues in Perl
- Description: Multiple issues in Perl were addressed in this update.
- CVE-2018-12015: Jakub Wilk
- CVE-2018-18311: Jayakrishna Menon
- CVE-2018-18313: Eiichi Tsukata
QuartzCore
- Available for: macOS Mojave 10.14.3
- Impact: A malicious application may be able to execute arbitrary code with system privileges
- Description: Multiple input validation issues existed in MIG generated code. These issues were addressed with improved validation.
- CVE-2019-8549: Mohamed Ghannam (@_simo36) of SSD Secure Disclosure (ssd-disclosure.com)
Security
- Available for: macOS Mojave 10.14.3
- Impact: Processing malicious data may lead to unexpected application termination
- Description: Multiple memory corruption issues were addressed with improved input validation.
- CVE-2019-8507: Kai Lu of Fortinet’s FortiGuard Labs
Security
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: An application may be able to gain elevated privileges
- Description: A use after free issue was addressed with improved memory management.
- CVE-2019-8526: Linus Henze (pinauten.de)
Siri
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: A malicious application may be able to read restricted memory
- Description: An out-of-bounds read was addressed with improved bounds checking.
- CVE-2019-8520: Antonio Groza, The UK’s National Cyber Security Centre (NCSC)
Time Machine
- Available for: macOS Mojave 10.14.3
- Impact: A malicious application may be able to initiate a Dictation request without user authorization
- Description: An API issue existed in the handling of dictation requests. This issue was addressed with improved validation.
- CVE-2019-8502: Luke Deshotels of North Carolina State University, Jordan Beichler of North Carolina State University, William Enck of North Carolina State University, Costin Carabaș of University POLITEHNICA of Bucharest, and Răzvan Deaconescu of University POLITEHNICA of Bucharest
TrueTypeScaler
- Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
- Impact: A local user may be able to execute arbitrary shell commands
- Description: This issue was addressed with improved checks.
- CVE-2019-8513: CodeColorist of Ant-Financial LightYear Labs
XPC
- Available for: macOS Mojave 10.14.3
- Impact: Processing a maliciously crafted font may result in the disclosure of process memory
- Description: An out-of-bounds read was addressed with improved bounds checking.
- CVE-2019-8517: riusksk of VulWar Corp working with Trend Micro Zero Day Initiative
- Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
- Impact: A malicious application may be able to overwrite arbitrary files
- Description: This issue was addressed with improved checks.
- CVE-2019-8530: CodeColorist of Ant-Financial LightYear Labs
 Additional recognitionAccounts
Additional recognitionAccountsBooks
- We would like to acknowledge Milan Stute of Secure Mobile Networking Lab at Technische Universität Darmstadt for their assistance.
Kernel
- We would like to acknowledge Yiğit Can YILMAZ (@yilmazcanyigit) for their assistance.
- We would like to acknowledge Brandon Azad of Google Project Zero for their assistance.
Time Machine
- We would like to acknowledge Craig Young of Tripwire VERT and Hanno Böck for their assistance.
- We would like to acknowledge CodeColorist of Ant-Financial LightYear Labs for their assistance.
Information about products not manufactured by Apple, or independent websites not controlled or tested by Apple, is provided without recommendation or endorsement. Apple assumes no responsibility with regard to the selection, performance, or use of third-party websites or products. Apple makes no representations regarding third-party website accuracy or reliability. Risks are inherent in the use of the Internet. Contact the vendor for additional information. Other company and product names may be trademarks of their respective owners.公開日:
macOS Mojave 10.14.4への手動アップデート手順
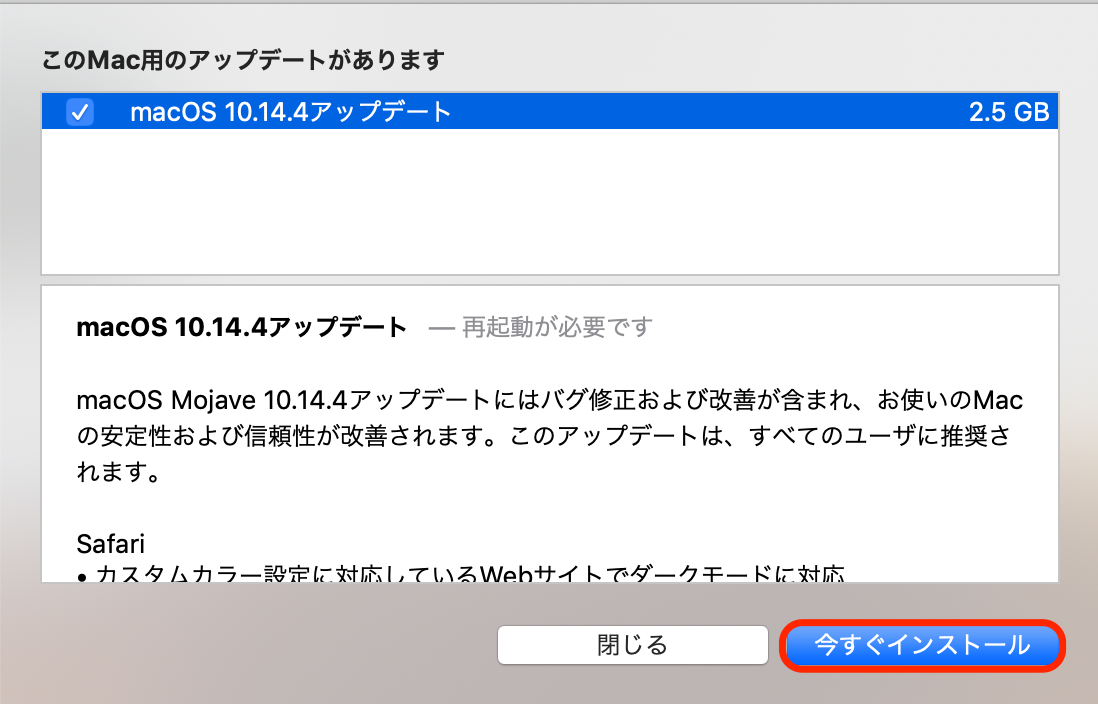
macOS Mojave 10.14.4への手動でのアップデート手順は次の通りです。 [timeline] [tl label=’手順 1′ title=’システム環境設定の起動’] 歯車のマークのアイコンをクリックし、システム環境設定を起動します。 [/tl][tl label=’手順 2′ title=’ソフトウェア・アップデートの起動’] システム環境設定画面の中で同じく歯車のマークのアイコンをクリックし、ソフトウェア・アップデートを起動します。 [/tl][tl label=’手順 3′ title=’アップデートの開始’]
ソフトウェア・アップデート画面で「今すぐアップデート」ボタンをクリックし、アップデートを開始します。
[/tl][tl label=’手順 3′ title=’アップデートの開始’]
ソフトウェア・アップデート画面で「今すぐアップデート」ボタンをクリックし、アップデートを開始します。
 [/tl][tl label=’手順 4′ title=’アップデートの続行’]
アップデートがダウンロードされていない場合は「macOS 10.14.4アップデート」の行が表示されるので、チェックマークにチェックが入っていることを確認し「今すぐアップデート」ボタンをクリックします。
[/tl][tl label=’手順 4′ title=’アップデートの続行’]
アップデートがダウンロードされていない場合は「macOS 10.14.4アップデート」の行が表示されるので、チェックマークにチェックが入っていることを確認し「今すぐアップデート」ボタンをクリックします。
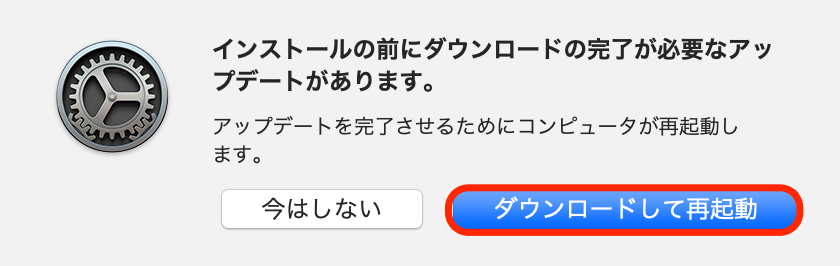
 [/tl][tl label=’手順 5′ title=’アップデートの続行’]
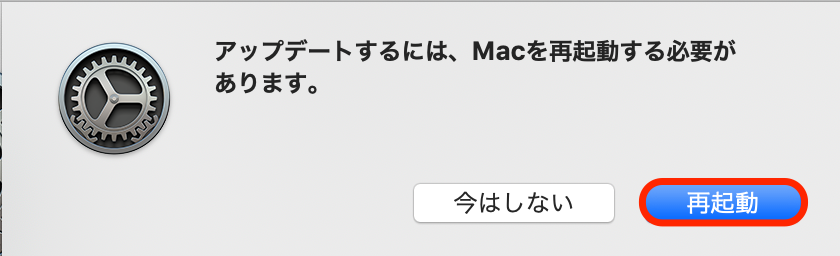
再起動が必要なという確認画面が表示されるので、「ダウンロードして再起動」をクリックします。
[/tl][tl label=’手順 5′ title=’アップデートの続行’]
再起動が必要なという確認画面が表示されるので、「ダウンロードして再起動」をクリックします。
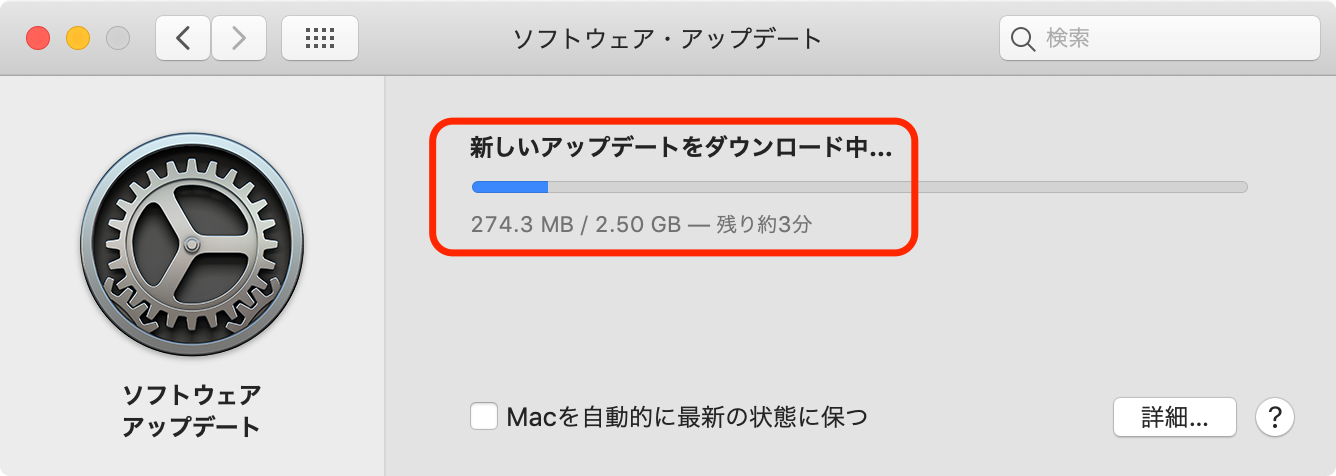
 [/tl][tl label=’手順 6′ title=’ダウンロードの実施’]
新しいアップデートがMacにダウンロードされます。
[/tl][tl label=’手順 6′ title=’ダウンロードの実施’]
新しいアップデートがMacにダウンロードされます。
 [/tl][tl label=’手順 7′ title=’アップデートの続行’]
ダウンロードが完了するとソフトウェア・アップデート画面が再度表示されるので「今すぐアップデート」をクリックします。
[/tl][tl label=’手順 7′ title=’アップデートの続行’]
ダウンロードが完了するとソフトウェア・アップデート画面が再度表示されるので「今すぐアップデート」をクリックします。
 [/tl][tl label=’手順 8′ title=’アップデートの続行’]
再起動が必要という確認画面が表示されるので「再起動」ボタンをクリックします。
[/tl][tl label=’手順 8′ title=’アップデートの続行’]
再起動が必要という確認画面が表示されるので「再起動」ボタンをクリックします。
 [/tl][tl label=’手順 9′ title=’アップデートの確認’]
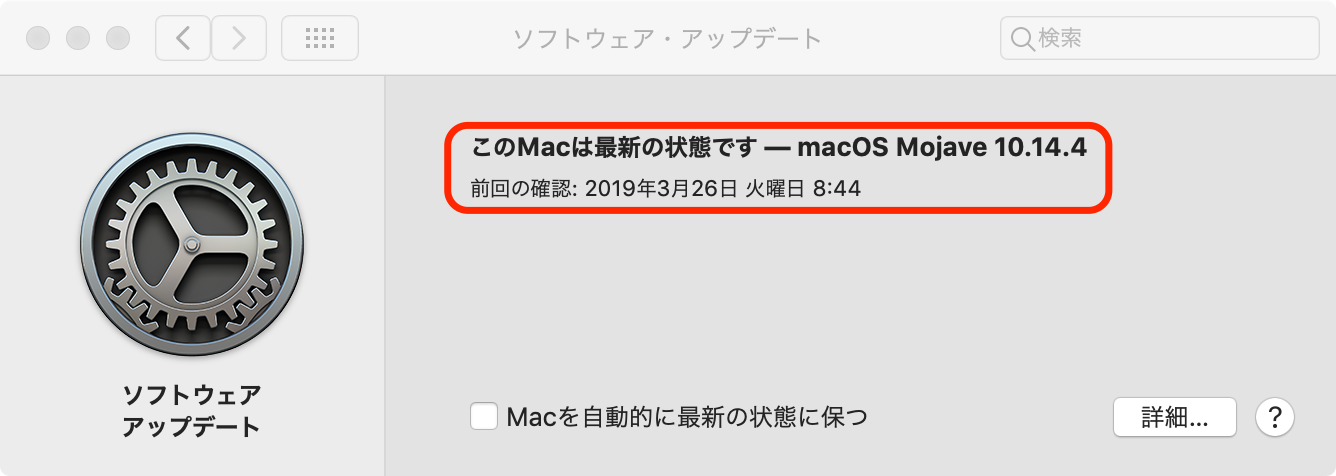
再起動ならびにインストールが実施された後、ログイン画面が表示されるのでログインするとソフトウェア・アップデート画面が表示されます。
「このMacは最新の状態です - macOS Mojave 10.14.4」と表示されることを確認します。
[/tl][tl label=’手順 9′ title=’アップデートの確認’]
再起動ならびにインストールが実施された後、ログイン画面が表示されるのでログインするとソフトウェア・アップデート画面が表示されます。
「このMacは最新の状態です - macOS Mojave 10.14.4」と表示されることを確認します。
 [/tl][tl title=’完了’][/tl][/timeline]
[/tl][tl title=’完了’][/tl][/timeline]
macOS Mojave 10.14.4にアップデートされたことの確認方法(オプション)
ソフトウェア・アップデート画面に10.14.4である旨か表示されればアップデートは完了しています。 その他にアップデートされたことを確認するには次の手順で実施します。このMacについて画面での確認
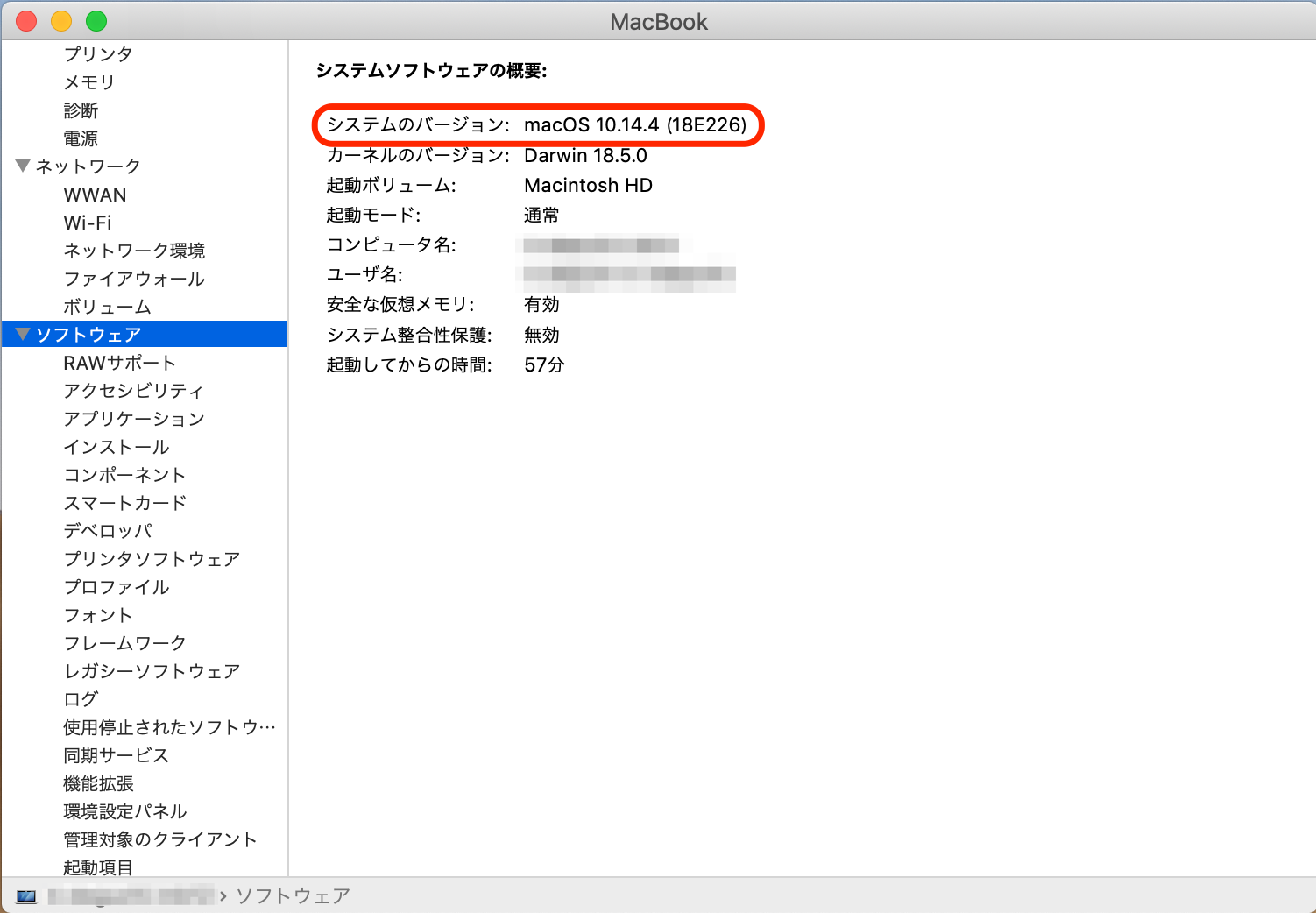
[timeline] [tl label=’手順 1′ title=’メニューバーのリンゴマークをクリック’][/tl] [tl label=’手順 2′ title=’「このMacについて」をクリック’][/tl] [tl label=’手順 3′ title=’macOS 10.14.4であることの確認’] 概要画面に「macOS Mojave バージョン10.14.4」と表示されることを確認します。 さらに確認するには、「システムレポート」ボタンをクリックし、表示された画面の左ペインのツリーから「ソフトウェア」をクリックします。
右ペインの「システムソフトウェアの概要」の「システムのバージョン」が「macOS 10.14.4 (18E226)」と表紙されることを確認します。
さらに確認するには、「システムレポート」ボタンをクリックし、表示された画面の左ペインのツリーから「ソフトウェア」をクリックします。
右ペインの「システムソフトウェアの概要」の「システムのバージョン」が「macOS 10.14.4 (18E226)」と表紙されることを確認します。
 以上です。
[/tl][tl][/tl][/timeline]
以上です。
[/tl][tl][/tl][/timeline]